Welcome to the latest edition of the Xygeni Malicious Code Digest (Monthly Edition). Once again, our security team analyzed real package telemetry across public registries to identify what traditional scanners often overlook: malicious code designed to blend into trusted developer workflows.
Over the past few weeks, we confirmed more than 270 malicious packages, primarily across npm, with additional cases affecting PyPI, VS Code, and OpenVSX. However, this month was not only about volume.
Our research team conducted in-depth analysis into high-impact threats, including:
The LiteLLM Supply Chain Attack, where compromised security tooling was used to backdoor AI infrastructure and distribute malicious code through a widely trusted dependency chain:
Recurring malware waves built around fake internal tooling, AI-themed packages, SDK impersonation, frontend components, builder utilities, and repeated version bursts under the same package families.
These were not simple typosquatting attempts. They involved credential abuse, supply chain manipulation, repeated namespace abuse, and malicious publishing patterns designed to impact real CI/CD pipelines and production environments.
Beyond these investigations, recent waves continued to show automation-driven publishing, aggressive version inflation, internal-tool impersonation patterns, and package clustering across related names, alongside classic tactics such as typosquatting, dependency confusion, and data exfiltration. The objective remains consistent: bypass trust heuristics and quietly compromise developer systems before detection.
This monthly update is part of our ongoing malware report, where we publish validated findings, confirm emerging threats, and provide actionable intelligence to help DevSecOps teams stay ahead of supply chain risk.
For full context across every malicious package analyzed this month, explore the complete Malicious Code Digest.
Week 3: Over 220 Packages Discovered
| Ecosystem | Package | Date |
|---|---|---|
| pypi | parascode:1.1.2 | Mar 27, 2026 |
| npm | @ctfsolve9z/coral-wraith:9999.0.2 | Mar 25, 2026 |
| npm | coral-wraith:9999.0.2 | Mar 25, 2026 |
| npm | wraith-of-war:9999.0.0 | Mar 25, 2026 |
| npm | stormbreaker-shade:9999.0.3 | Mar 25, 2026 |
| npm | coral-wraith:9999.0.8 | Mar 25, 2026 |
| npm | ghost-engine:99.0.0 | Mar 25, 2026 |
| npm | ecto-phantom:99.0.0 | Mar 25, 2026 |
| npm | ecto-engine:99.0.0 | Mar 25, 2026 |
| npm | corsair-module:99.0.0 | Mar 25, 2026 |
Week 2: Over 11 Packages Discovered
| Ecosystem | Package | Date |
|---|---|---|
| npm | spectral-corsair-navigator:99.99.100 | Mar 16, 2026 |
| npm | spectral-corsair-my-backdoor:99.99.101 | Mar 16, 2026 |
| npm | lint-builder:1.0.0 | Mar 20, 2026 |
| npm | testpoc01:1.0.0 | Mar 16, 2026 |
| npm | ember-power-calendar-utils:99.9.91 | Mar 17, 2026 |
| npm | devlino:1.0.4 | Mar 16, 2026 |
| npm | devlino:1.0.6 | Mar 16, 2026 |
| npm | devlino:1.0.8 | Mar 16, 2026 |
| npm | graphql-request-dom:1.0.7 | Mar 16, 2026 |
| npm | devlino:1.0.10 | Mar 16, 2026 |
| npm | @wealth-common/font:99.0.3 | Mar 16, 2026 |
Week 1: Over 40 Packages Discovered
| Ecosystem | Package | Date |
|---|---|---|
| npm | naughty-package:1.0.2 | Mar 02, 2026 |
| npm | piyush_test_vadapav:1.0.1 | Mar 01, 2026 |
| npm | replay-ci:1.0.0 | Mar 02, 2026 |
| npm | replay-ci:1.0.1 | Mar 02, 2026 |
| npm | ng-vzbootstrap:1.0.3 | Mar 03, 2026 |
| npm | naughty-package:1.0.6 | Mar 02, 2026 |
| npm | pdfjs-dist-v5:100.21.1 | Mar 03, 2026 |
| npm | pino-sdk:9.9.0 | Mar 04, 2026 |
| npm | aio-security-test-template-erk1ny:1.0.0 | Mar 04, 2026 |
| npm | pino-sdk-v2:9.9.0 | Mar 04, 2026 |
Secure Your Open Source Dependencies against Vulnerabilities and Malicious Code
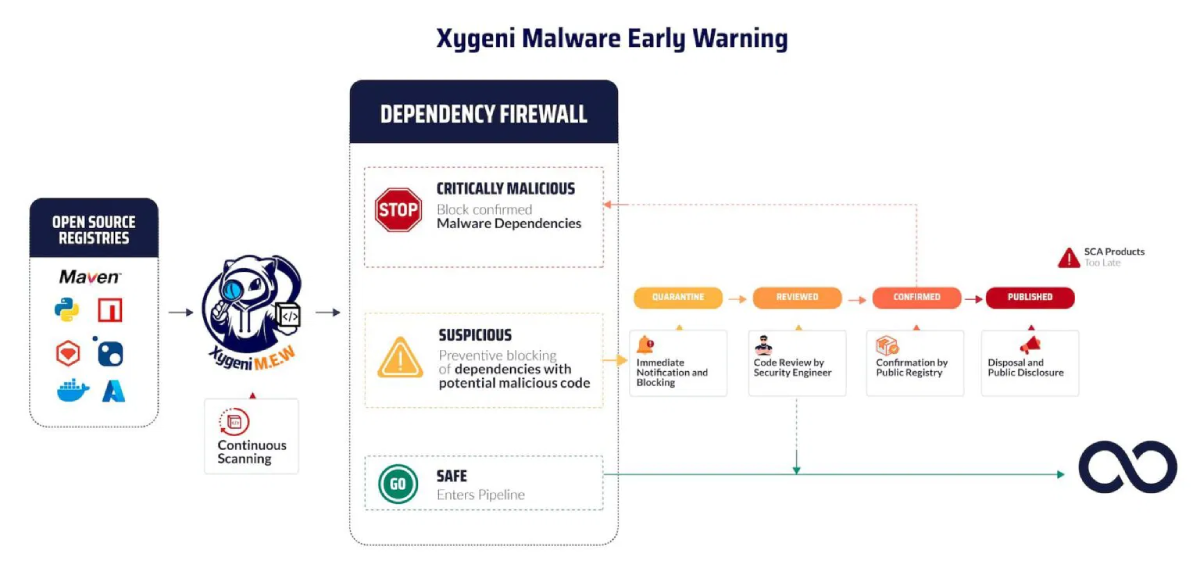
Malware isn’t just a theoretical risk anymore, it’s already hiding in public packages. With Xygeni’s Early Malware Detection, you can reduce exposure by catching threats as soon as they’re published, before they reach your pipeline.
Our real-time scanning and prioritization engine continuously monitors public registries like npm and PyPI. Malicious packages are blocked, flagged, and ranked based on impact, so you know exactly what needs fixing, and when. Whether it’s typosquatting, dependency confusion, or credential stealers, we help your team stay ahead.
If you want full visibility into weekly and monthly findings, check the complete Malicious Code Digest.
Stay secure. Stay fast. Stay in control with Xygeni.