Every week, our malware detection systems scan thousands of new and updated packages across public registries like npm and PyPI.
This week was different.
Beyond confirming 34+ malicious packages, our research team conducted in-depth investigations into:
- A newly uncovered infostealer campaign abusing the npm ecosystem
- A malicious fork targeting the Baileys WhatsApp library supply chain
These were not simple typosquatting cases. Both involved credential abuse and session hijacking techniques capable of impacting real developer environments.
This weekly snapshot is part of our ongoing Malicious Code Digest, where we validate new threats and provide actionable intelligence to help DevSecOps teams protect their pipelines before damage occurs.
Let’s break down what we found this week and why it matters.
| Ecosystem | Package | Date |
|---|---|---|
| npm | uxproject11:1.0.0 | Feb 23, 2026 |
| npm | opencraw:2026.2.15 | Feb 20, 2026 |
| npm | react-dropzone-truffle:100.21.9 | Feb 23, 2026 |
| npm | drikssy-sdk-test:1.0.8 | Feb 23, 2026 |
| npm | @powpegtest/powpeg:10.2.0 | Feb 23, 2026 |
| npm | eslint-validator:1.0.2 | Feb 23, 2026 |
| npm | selfbot-lofy:1.2.5 | Feb 23, 2026 |
| npm | ng-vzbootstrap:1.0.1 | Feb 23, 2026 |
| npm | ng-vzbootstrap:1.0.2 | Feb 23, 2026 |
| npm | vds-monarch:1.0.4 | Feb 23, 2026 |
| npm | consolelofy:1.2.7 | Feb 23, 2026 |
| npm | conduit-utils:2.95.0 | Feb 22, 2026 |
| npm | conduit-utils:2.96.0 | Feb 23, 2026 |
| npm | conduit-utils:2.97.0 | Feb 23, 2026 |
| npm | conduit-utils:2.98.0 | Feb 23, 2026 |
| npm | conduit-utils:2.99.0 | Feb 23, 2026 |
| npm | conduit-utils:3.99.0 | Feb 23, 2026 |
| npm | en-thrift-internal:2.99.9 | Feb 25, 2026 |
| npm | corp-build-utils-poc:99.9.11 | Feb 23, 2026 |
| npm | corp-build-utils-poc:99.9.14 | Feb 23, 2026 |
| npm | launch-darkly-js:199.99.99 | Feb 23, 2026 |
| npm | @dappaoffc/baileys-mod:8.0.1 | Feb 24, 2026 |
| npm | unibody:99.9.9 | Feb 27, 2026 |
| npm | rncalendareventsexample:0.0.5 | Feb 27, 2026 |
| npm | examplereactnative76:0.0.8 | Feb 27, 2026 |
| npm | rncalendareventsexample:0.0.10 | Feb 27, 2026 |
| npm | test-mal-npm-pkg-local:1.0.0 | Feb 27, 2026 |
| npm | launch-darkly-js:199.99.102 | Feb 27, 2026 |
| npm | launch-darkly-js:199.99.103 | Feb 27, 2026 |
| npm | consolelofy:1.3.0 | Feb 26, 2026 |
| npm | test-mal-npm-pkg-2:1.0.0 | Feb 27, 2026 |
| npm | launch-darkly-js:199.99.106 | Feb 27, 2026 |
| npm | foundry-toolkit:1.0.5 | Feb 27, 2026 |
| npm | foundry-toolkit:1.0.13 | Feb 27, 2026 |
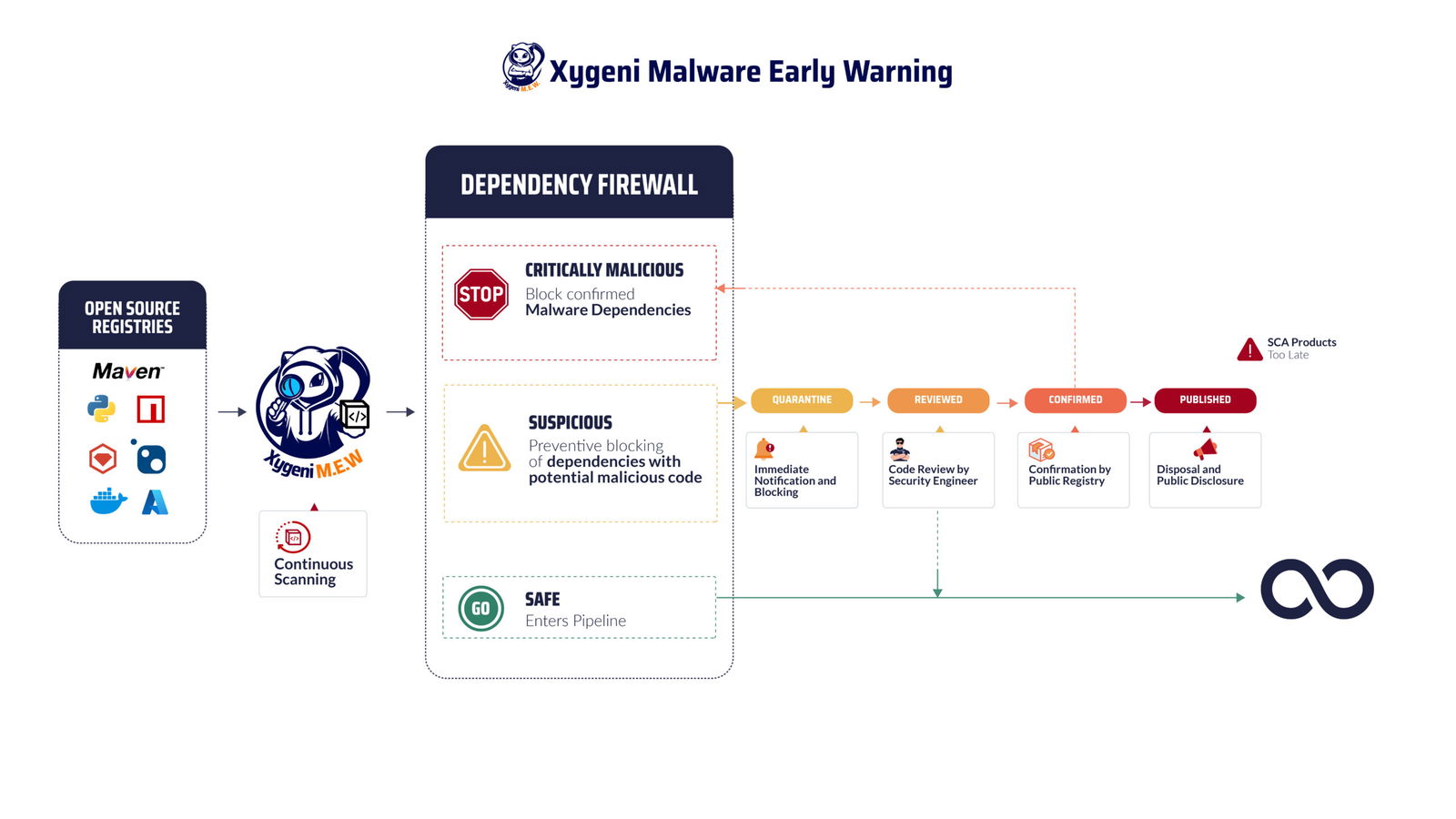
Secure Your Open Source Dependencies against Vulnerabilities and Malicious Code
Minimize risks and protect your applications from malicious packages with Xygeni Early Malware Detection. Prioritize and address the vulnerabilities that matter most. Our comprehensive solution offers real-time monitoring of your dependencies to detect and mitigate threats before they impact your software.
Managing open-source components in the current software development landscape is crucial due to the rising vulnerabilities and malicious code threats. Xygeni’s Open Source Security solution scans and blocks harmful packages upon publication, dramatically minimizing the risk of malware and vulnerabilities infiltrating your systems. Our comprehensive monitoring spans multiple public registries, ensuring all dependencies are scrutinized for safety and integrity. Xygeni enhances your team’s ability to maintain secure and reliable software projects by contextually prioritizing critical issues and facilitating streamlined remediation processes.
Xygeni uses multi-layered techniques to stop malicious code before it spreads. First of all, static code analysis detects obfuscation patterns, hidden payloads, and script abuse. In addition, behavioral sandboxing analyzes install hooks, runtime commands, and persistence tricks. Moreover, machine learning detection identifies zero-day npm malware and pypi malware variants missed by signature scanners. Finally, the Early Warning System monitors public repositories in real time, validates findings, and alerts DevOps teams immediately.
As a result, this combination ensures developers receive fast, actionable intelligence integrated directly into CI/CD workflows.
Why Developers Should Care About Malicious npm Packages
Modern threats rarely wait for runtime. For example, malicious npm packages often execute during installation, while pypi malicious packages hide token exfiltration or backdoors. Attackers:
- Flip private GitHub repos to public to replicate them.
- Exfiltrate credentials and secrets using encoded payloads.
- Use obfuscated JavaScript loaders to deploy ransomware or botnets.
In fact, malicious open-source packages surged 156% in one year. Therefore, teams that rely only on delayed feeds or basic scanners fall behind.
What This Malware Report Tracks in npm and PyPI
This digest is the central hub for:
- Confirmed malicious npm packages
- Confirmed pypi malicious packages
- Behavior-based detections of malicious code
- Registry-confirmed incidents
- Weekly and monthly malware report summaries
- Historical changelog of all npm malware and pypi malware findings
In other words, it provides a single point of reference. The research team at Xygeni updates this page weekly with links to full technical analyses and GitHub IOCs.
How to Protect Against Malicious npm Packages and PyPI Malware
Because of this growing risk, organizations need strong defenses:
- Enforce lockfile-only installs (
npm ci) in CI/CD. - Additionally, scan dependencies pre-install with Xygeni’s Early Warning Engine.
- Furthermore, block builds on malicious code signals using Guardrails.
- Generate SBOMs to trace indirect dependencies and apply policies.
- Above all, train developers to detect typosquatting, obfuscation, and suspicious install scripts.
Try Xygeni’s Malware Detection Tools
Xygeni delivers:
- Real-time detection of malicious code, including backdoors, spyware, and ransomware.
- In contrast to basic scanners, analysis across npm, PyPI, Maven, NuGet, RubyGems, and more.
- Automatic build blocking when the malware report identifies risk.
- Exploitability insights, maintainer reputation checks, and anomaly detection.